
The largest NPM attack in crypto history targeted popular JavaScript libraries in a massive supply chain breach.
Despite the scope, less than $50 in crypto was stolen, primarily ETH and memecoins.
Affected libraries were widely used, even in projects that didn’t directly install them.
Malware functioned as a crypto clipper, silently swapping wallet addresses.
Major platforms like MetaMask and Ledger remain unaffected.
Security experts discovered that the malware was a crypto clipper, a type of malicious code that silently alters copied wallet addresses, redirecting funds to the attacker’s wallet during crypto transactions.
Samczsun, a pseudonymous researcher from SEAL, said:
“The hacker didn’t fully capitalize on the access they had, it’s like finding the keycard to Fort Knox and using it as a bookmark.”
The malware has reportedly been neutralized in most environments, and no ongoing threat has been identified beyond the initial infection.
Initially, only five cents worth of ETH was reported stolen, despite the fact that the hacker had access to potential millions.
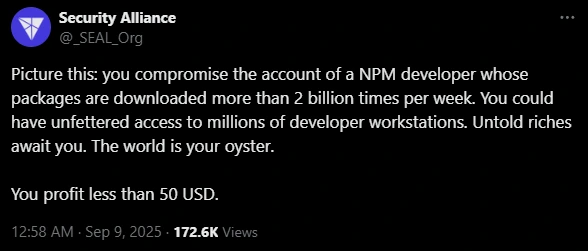
Source: X (@_SEAL_Org)
That number later rose to around $50, including a mix of small-cap memecoins like:
Brett (BRETT)
Andy (ANDY)
Dork Lord (DORK)
Ethervista (VISTA)
Gondola (GONDOLA)
All funds were funneled into the same malicious wallet address identified by the researchers.
Even crypto projects that did not directly download the compromised packages may still be at risk if their dependencies pulled in infected code.
This includes:
Wallet applications
Backend services interfacing with blockchain networks
Many major platforms have confirmed they are not impacted by the NPM attack, including:
Ledger
Uniswap
Phantom Wallet
Aerodrome
Blockstream Jade
Revoke.cash
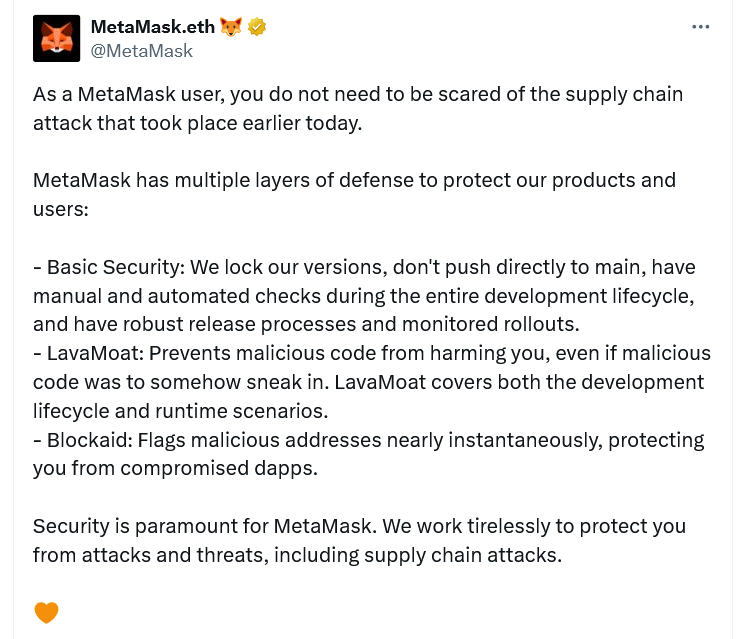
Source: X (@MetaMask)
These platforms credit their multi-layered defense systems and thorough dependency audits for their resilience against the supply chain breach.
Despite the low amount stolen so far, industry experts warn users to remain cautious.
0xngmi, founder of DefiLlama, said:
“Users won’t be instantly drained, but any project that updated their code after the malware was published could potentially be vulnerable, especially if users approve malicious transactions.”
Until a full cleanup is confirmed, it’s wise for crypto users and developers alike to:
Avoid interacting with dApps that may have recently updated dependencies
Double-check wallet addresses before confirming transactions
Monitor project updates for disclosures related to the NPM breach
An NPM attack involves injecting malicious code into packages distributed via the Node Package Manager. Because many apps rely on NPM packages, a single compromised package can affect thousands of projects.
While exact details are unclear, it’s likely the attacker obtained access credentials through phishing, credential stuffing, or poor account hygiene.
If you’ve interacted with a dApp or wallet app that recently updated packages like chalk or strip-ansi, you may be at risk. Watch for unusual transactions and consider revoking permissions using tools like Revoke.cash.
A crypto clipper is malware that replaces a copied wallet address with the attacker’s address when you paste it into a transaction — silently redirecting your funds.
No. As of now, the malware has been largely neutralized. However, residual risks may exist in projects that haven’t yet updated their dependencies.
Subscribe to stay informed and receive latest updates on the latest happenings in the crypto world!

Content Strategist
Subscribe to stay informed and receive latest updates on the latest happenings in the crypto world!
 Figure Heloc(FIGR_HELOC)$1.030.16%
Figure Heloc(FIGR_HELOC)$1.030.16% USDS(USDS)$1.000.01%
USDS(USDS)$1.000.01% Hyperliquid(HYPE)$45.183.71%
Hyperliquid(HYPE)$45.183.71% Ethena USDe(USDE)$1.00-0.01%
Ethena USDe(USDE)$1.00-0.01% Canton(CC)$0.147645-1.95%
Canton(CC)$0.147645-1.95% MemeCore(M)$2.85-0.94%
MemeCore(M)$2.85-0.94% USD1(USD1)$1.000.10%
USD1(USD1)$1.000.10% Rain(RAIN)$0.007772-2.82%
Rain(RAIN)$0.007772-2.82% RaveDAO(RAVE)$14.670.85%
RaveDAO(RAVE)$14.670.85% Circle USYC(USYC)$1.120.00%
Circle USYC(USYC)$1.120.00% World Liberty Financial(WLFI)$0.0809781.44%
World Liberty Financial(WLFI)$0.0809781.44% BlackRock USD Institutional Digital Liquidity Fund(BUIDL)$1.000.00%
BlackRock USD Institutional Digital Liquidity Fund(BUIDL)$1.000.00% Bittensor(TAO)$242.00-1.22%
Bittensor(TAO)$242.00-1.22% Global Dollar(USDG)$1.000.02%
Global Dollar(USDG)$1.000.02% Falcon USD(USDF)$1.00-0.04%
Falcon USD(USDF)$1.00-0.04% Sky(SKY)$0.0748920.68%
Sky(SKY)$0.0748920.68% Pi Network(PI)$0.1703042.07%
Pi Network(PI)$0.1703042.07%